CYBER THREAT INTELLIGENCE
Become a
Cyber Threat Intelligence Analyst (CTIA)
"*" indicates required fields
"*" indicates required fields






"*" indicates required fields

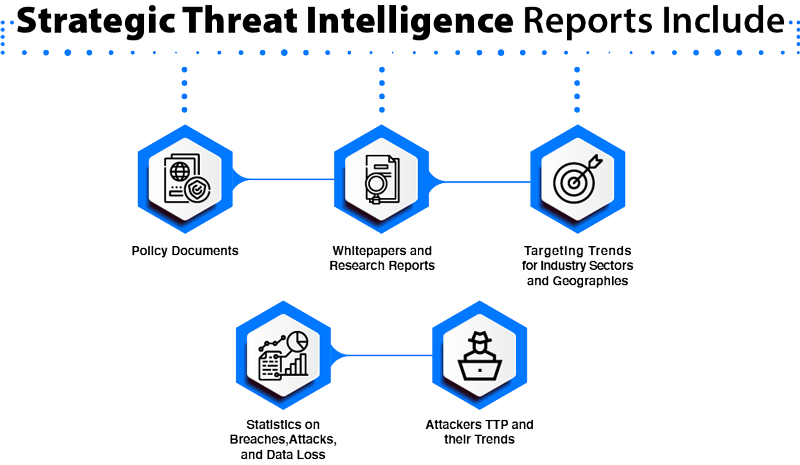
Strategic threat intelligence provides an overview of the organization’s threat landscape. It is less technical is mainly for executive-level security professionals to drive high-level organizational strategy based on the findings in the reports. Ideally, strategic threat intelligence provides insights like vulnerabilities and risks associated with the organization’s threat landscape with preventive actions, threat actors, their goals, and the severity of the potential attacks.
Tactical threat intelligence consists of more specific details on threat actors TTP and is mainly for the security team to understand the attack vectors. Intelligence gives them insights on how to build a defense strategy to mitigate those attacks. The report includes the vulnerabilities in the security systems that attackers could take advantage of and how to identify such attacks.
The finding is used to strengthen the existing security controls/defense mechanism and helps to remove the vulnerabilities in the network.
Technical threat intelligence focuses on specific clues or evidence of an attack and creates a base to analyze such attacks. Threat Intelligence analyst scans for the indicator of compromise (IOCs), which includes reported IP addresses, the content of phishing emails, malware samples, and fraudulent URLs. Timing for sharing technical intelligence is very critical because IOCs such as malicious IPs or fraudulent URLs become obsolete in a few days.
Operational threat intelligence focuses on knowledge about the attacks. It gives detailed insights on factors like nature, motive, timing, and how an attack is carried out. Ideally, the information is gathered from hacker chat rooms or their discussion online through infiltration, which makes it difficult to obtain.
Cyber Threat Intelligence program combines thousands of Threat Intelligence Feeds into a single feed, instead of viewing them separately to enable consistent characterization and, categorization of cyber threat events, and identify trends or changes in the activities of cyber adversaries. The program consistently describes cyber threat activity in a way that allows efficient information sharing and threat analysis. It assists the threat intelligence team by comparing the feed with internal telemetry and creates alerts.


Cyber intelligence analysts, also known as “cyber threat analysts,” are information security professionals who use their skills and background knowledge to collect and analyze the threat data to create intelligence in the form of reports and share with the respective department. Certified cyber intelligence analyst is required for creating a threat intelligence program.
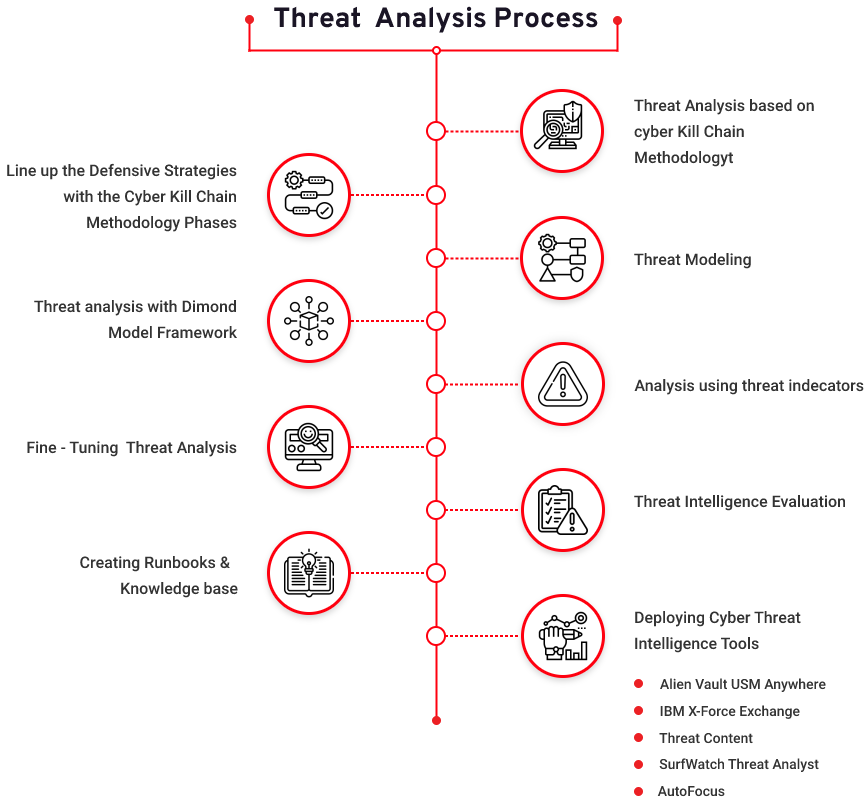
Threat intelligence strategy involves sound planning with the application of tools, techniques, and methodologies, followed by a review to check the effectiveness of the plan. While devising the strategy, one should also consider their threat intelligence capabilities and structure the program accordingly, including the support of different departments.
Understanding cyber threats and advanced persistent threats are the most crucial aspect of threat intelligence program.
The cyber kill chain is a series of steps that trace stages of a cyberattack from the early reconnaissance stages to the exfiltration of data. The kill chain helps us understand and combat ransomware, security breaches, and advanced persistent attacks (APTs)
Cyber Threat Intelligence Data Collection and Acquisition
Collecting relevant threat data for analysis and processing is an important step for creating cyber threat intelligence. The data is collected from various sources using predefined TTP (Tactics, Techniques and Procedures). Few sources of data are internal like network logs, past cyber incidents, and security landscape. The external source includes threat feeds, communities, forums, open web, and dark web.

According to a report by Grand View Research, Inc., the market for threat intelligence will reach $12.6 billion by 2025. This clearly shows the growing demand for cyber threat intelligence experts. In the future, there is enormous scope for threat intelligence services with the growing demand.
Companies, although investing generously in their cybersecurity solutions, remain susceptible to cyber-attacks, and this is an alert to help us realize that the traditional cybersecurity approach must be replaced with new and effective solutions, one of them is “cyber threat intelligence – a proactive approach to predictive analysis.”
A career in cyber threat intelligence has several number of avenues in the space of cybersecurity, and essentially there is a need for security professionals with skills in threat intelligence due to the evolving security landscape.
As per LinkedIn, over 10,000 Threat Intelligence jobs are vacant worldwide, which recounts a huge demand for threat intelligence professionals globally and will significantly influence and shape the face of cybersecurity.
On average cyber threat intelligence analyst’s salary in the United States is $75,000, and they typically make between $51k – $140k.











CTIA is a comprehensive program that teaches a structured approach for creating actionable intelligence and covers the topics starting from planning to creating reports and disseminating intelligence. The program is developed by cyber intelligence experts and help organizations identify vulnerabilities and risk to take preventive measures, and protect the business from future cyberattacks. The program addresses all the stages of threat intelligence lifecycle topics covered in the program that are essential for building a threat intelligence program
EC-Council has a repository of learning resources and is not limited to the Threat Intelligence domain. Here is the list of resources, a). EC-Council Free Resources, b). EC-Council Blogs, c). EC-Council Whitepaper, d). EC-Council Cyber Talks
"*" indicates required fields